Tax Season Phishing Scams and Cyber Liability Risks for Michigan Nonprofits
Posted on January 30, 2026
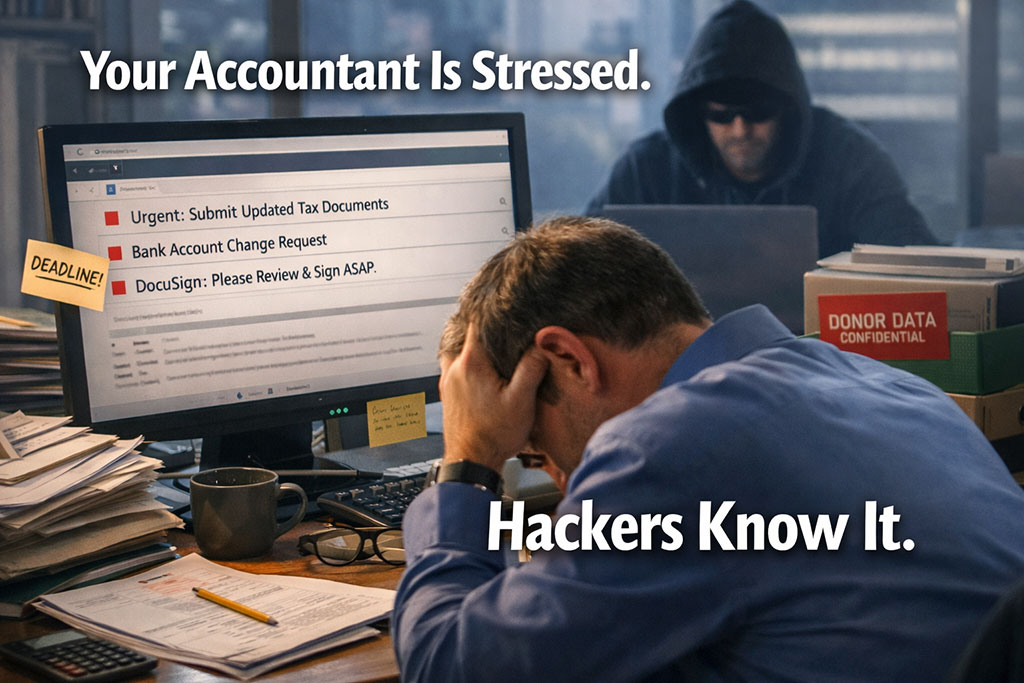
It’s March in Metro Detroit.
Your finance director is buried in reconciliations.
Your bookkeeper is issuing donor tax receipts.
Your development team is answering year-end giving questions.
Your CPA is moving fast.
And your inbox is overflowing.
If you’re a nonprofit leader in Michigan, this season feels intense — every year.
But here’s what many organizations don’t realize:
Tax season is peak phishing season.
Cybercriminals specifically target nonprofits, accounting teams, and finance staff during March and April — because they know your team is moving quickly.
And when teams move quickly, cyber liability exposure increases.
Let’s walk through what that really means for your organization — and how to reduce the risk calmly and confidently.
Why Tax Season Increases Phishing Attacks on Nonprofits
Security researchers consistently report a sharp spike in tax-related phishing emails during Q1. In March alone, tax-themed scam emails increase by nearly 30%.
These emails are designed to look ordinary:
- “Please resend W-2 documents.”
- “Vendor ACH information has changed.”
- “Urgent DocuSign request.”
- “Quick help needed while I’m traveling.”
They blend perfectly into nonprofit workflows.
For Michigan nonprofits managing donor CRMs, online giving platforms, and payroll systems, the risk isn’t just an annoying scam.
It’s potential cyber liability exposure — meaning business, legal, regulatory, and operational risk if cybersecurity responsibilities aren’t fully met.
Here’s what that can trigger:
- Donor trust damage
- Michigan data breach notification requirements
- Cyber insurance claim scrutiny
- Board-level accountability conversations
- Funders questioning stewardship practices
That’s not fear talk. That’s stewardship reality.
The “Stressed Supply Chain” Effect in Nonprofits
Hackers aren’t just targeting CPAs.
They target the entire nonprofit ecosystem during tax season:
- Finance teams sending payroll files
- Development teams exporting donor data
- Vendors submitting updated payment details
- Executives approving wire transfers
- Boards requesting updated financial summaries
When everything speeds up, verification slows down.
And speed is where mistakes happen.
Nonprofits often believe they’re “too small to be targeted.”
Unfortunately, attackers prefer small and mid-sized nonprofits because they often lack layered cybersecurity controls while still handling sensitive donor and financial data.
What a Tax Season Cyberattack Actually Looks Like
It rarely looks dramatic.
It looks like:
- A spoofed email from your CPA requesting payroll data
- A fake vendor asking to update ACH information
- A phishing link disguised as a donation platform alert
- An urgent message appearing to come from your executive director
If one staff member responds incorrectly, the fallout may include:
- Compromised donor data
- Fraudulent payments
- Regulatory reporting under Michigan breach law
- Increased cyber insurance premiums
- Operational downtime
That’s cyber liability in action — business risk, legal risk, regulatory risk, and operational disruption.
And it often starts with one rushed click.
Four Practical Cybersecurity Steps for Nonprofits During Tax Season
You don’t need enterprise-level complexity.
You need consistent, calm controls.
1. Verify Vendor Payment Changes by Phone
Never rely solely on email when bank information changes.
Call a known, trusted number to confirm.
This single step prevents many nonprofit fraud cases each year.
2. Require Multi-Factor Authentication (MFA)
If your donor CRM, payroll platform, or Microsoft 365 account doesn’t require MFA, your organization is exposed.
MFA dramatically reduces phishing success rates and is now expected by most cyber insurers.
3. Pause on Urgent Financial Requests
Train your staff to treat urgency as a signal to slow down.
Real urgency survives verification.
Fraud collapses under it.
4. Conduct a Quick Tax-Season Risk Review
Ask:
- Are backups tested?
- Is endpoint protection active?
- Do we have an incident response plan?
- Could we confidently answer our board’s cyber questions today?
If the answer feels uncertain, that’s not failure.
It’s an opportunity for improvement.
Why This Matters for Michigan Nonprofit Leaders
In Metro Detroit and across Michigan, nonprofit boards and funders are asking tougher cybersecurity questions:
- “Are we compliant with data protection expectations?”
- “Would cyber insurance pay out if we had an incident?”
- “Are we managing third-party vendor risk properly?”
Cyber liability is no longer an IT issue.
It’s a governance issue.
And governance lives at the board table.
Your role as a nonprofit leader isn’t to become a cybersecurity expert.
It’s to ensure you have the right protections in place — and the right documentation to prove it.
You don’t need to speak IT.
You need to speak stewardship.
The Takeaway: Calm Reduces Risk
Tax season phishing scams are not especially clever.
They’re just well-timed.
They rely on:
- Overloaded teams
- Tight deadlines
- Assumptions
- Good people moving too quickly
You can reduce your nonprofit’s cyber liability exposure without panic.
Slow down.
Verify.
Add layered protection.
Educate your team.
Confidence grows from clarity — not fear.
Schedule a Nonprofit Cyber Liability Discovery Call
If you’re a nonprofit leader in Metro Detroit or Southeast Michigan and you’re unsure whether your organization is protected during high-risk seasons like tax time, this is the right moment for a calm review.
We offer a brief Discovery Call to:
- Identify potential cyber liability exposure
- Review your current controls
- Clarify what boards and insurers expect
- Outline practical next steps
No scare tactics.
No tech jargon.
Just clear answers you can take to your board.
👉 Schedule your Discovery Call here:
https://go.appointmentcore.com/MTSDiscoveryCall
Your mission is too important to be disrupted by preventable cyber risk.
Let’s make sure you’re protected — calmly, confidently, and locally.